Bridge exploits and admin compromises drove most April losses, exposing critical weaknesses in DeFi infrastructure layers.
April 2026 marked a sharp escalation in crypto security breaches, with losses reaching $620 million across just 20 days. Activity spanned 12 separate incidents, making it the worst month since the Bybit breach in February 2025. Attack patterns ranged from social engineering to smart contract failures, with no single method dominating early on. Still, data shows a clear clustering of losses around a few critical weaknesses.
Total damages were 3.7 times higher than the combined total for all of Q1 2026. A significant portion of losses came from infrastructure-level vulnerabilities rather than isolated coding errors. Cross-chain bridges, admin access points, and collateral systems became primary targets. Attackers focused on areas where trust and automation intersect.
Early Crypto Hack Wave Driven by Social Engineering
According to DefiLlama, April opened with one of the largest incidents of the year. Drift Protocol suffered a $285 million exploit tied to long-term social engineering. Attackers spent months posing as a trading firm to build credibility with internal teams.
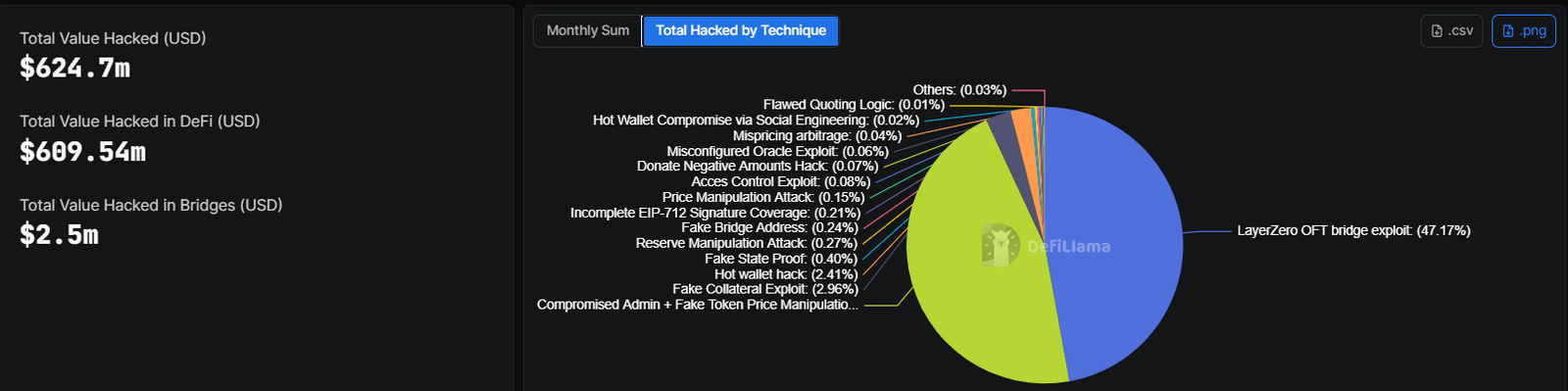
Image Source: DefiLlama
Access came through pre-signed transactions approved by Security Council members. Once control was gained, attackers deposited fake collateral and drained vaults within minutes. Reports linked the breach to North Korean hacking groups, adding geopolitical weight to the incident.
Smaller exploits followed quickly, as Silo Finance lost $392,000 due to an oracle misconfiguration. On the same day, Dango suffered a $410,000 loss tied to a smart contract bug. Both cases pointed to ongoing risks in protocol setup and auditing practices.
Pressure on liquidity pools increased after a $1.67 million exploit targeting BSC trading pairs. A flash loan attack on the BNB Chain followed, draining $1.6 million by manipulating reserves.
- Social engineering enabled deep system access without code-level exploits
- Oracle misconfigurations exposed lending protocols to pricing errors
- Flash loans allowed rapid reserve manipulation in low-liquidity pools
- Smart contract bugs remained a recurring but smaller contributor
Aethir lost $423,000, while SubQuery Network and Hyperbridge recorded combined losses exceeding $2.5 million. Attack surfaces expanded beyond core DeFi into infrastructure layers.
Domain hijacking added another dimension. CoW Swap lost $1.2 million after attackers took control of its domain. Zerion also reported a $100,000 exploit, showing frontend systems remain vulnerable.
Mid-Month Escalation Hits Exchanges and Lending
Mid-April saw a shift toward larger coordinated breaches. Grinex lost $13.74 million, with funds routed across dozens of wallets. The platform attributed the attack to foreign intelligence actors, though verification remains unclear.
At the same time, Rhea Lend recorded an $18.4 million exploit. Transaction analysis by Chainalysis suggested a possible exit scam, leaving uncertainty around intent.
Attention then shifted to cross-chain infrastructure. Kelp DAO suffered a $292 million exploit tied to a LayerZero bridge vulnerability. Attackers drained 116,500 rsETH in a single transaction, equal to 18% of the supply.
Impact spread quickly across DeFi lending markets. Aave now faces $177 million in bad debt linked to unliquidatable rsETH collateral. Credit risk has increased for one of the sector’s largest platforms.
Bridge-related exploits accounted for 47.17% of total losses during the month. Other methods remained fragmented, with each contributing less than 3% individually.
Late-Month Crypto Hack Activity Shows Systemic Weakness
Later incidents confirmed that vulnerabilities were not isolated. Juicebox and Thetanuts Finance lost modest amounts, while Volo Vault recorded a $3.5 million breach tied to vault design.
Further exploits hit Kipseli and Giddy, showing attackers continued targeting smaller platforms. Earlier losses from MONA added to the cumulative impact.
- Fake collateral exploits accounted for nearly 3% of total losses
- Fake state proof attacks exposed weaknesses in verification systems
- Reserve manipulation showed continued risk in automated market makers
- Signature validation gaps allowed unauthorized transaction approvals
Weekend activity added another case to the recent hacks. Purrlend lost $1.5 million after a suspicious multisig transaction granted unauthorized bridge access. Attackers exploited the new privileges within hours.
Cross-chain bridges remain a consistent point of failure. April’s data confirms that a small set of weaknesses drove most losses. Admin access, bridge infrastructure, and collateral systems carried the highest risk concentration.
Crypto security pressure continues to build as attackers refine methods across both on-chain and off-chain vectors.








Leave feedback about this